What the Heck Are TTPs? (And Why Every SOC Interview Asks About Them)
Learn what TTPs are, why MITRE ATT&CK matters, and how understanding them can help you land your first SOC job.
EpicDetect Team
5 min read

What the Heck Are TTPs? (And Why Every SOC Interview Asks About Them)
You're scrolling through SOC analyst job postings and keep seeing "knowledge of MITRE ATT&CK framework" and "understanding of adversary TTPs." But what does that actually mean? Let's break it down in plain English.
What Are TTPs?
TTPs stand for Tactics, Techniques, and Procedures. Think of them as the playbook attackers use.
- Tactics = The "why" (what's their goal?)
- Techniques = The "what" (how do they achieve it?)
- Procedures = The "how" (the specific steps they take)
Here's a real-world example: An attacker wants to steal credentials (that's the tactic). They might dump LSASS memory to grab password hashes (that's the technique). They use Mimikatz to do it (that's the procedure).
See? Not as scary as it sounds.
So What Is MITRE ATT&CK?
MITRE ATT&CK is basically a giant cheat sheet of every tactic and technique attackers use. It's organized, categorized, and constantly updated based on real-world attacks.
Think of it like a cookbook—except instead of recipes for chocolate chip cookies, it's recipes for credential dumping, lateral movement, and data exfiltration.
The framework has 14 tactics (like Initial Access, Persistence, Credential Access) and hundreds of techniques under each one. It sounds overwhelming, but here's the thing: you don't need to memorize all of it.
But Why Does Every SOC Job Want You to Know This?
Let's be honest: MITRE ATT&CK has become the universal language of cybersecurity.
When a SOC analyst says "we detected T1003 - OS Credential Dumping," everyone immediately knows what happened. No long explanations needed. It's like saying "the attacker stole passwords" but in a way that's precise and searchable.
Here's why employers care:
It Shows You Think Like a Defender
Understanding TTPs means you're not just looking at individual alerts—you're connecting the dots. You see a suspicious PowerShell command? Cool. But if you recognize it as part of T1059 (Command and Scripting Interpreter), you know what to look for next.
It Makes Communication Way Easier
Instead of saying "the attacker did this thing where they created a scheduled task to run a script every time the computer starts," you can just say "T1053 - Scheduled Task/Job for persistence." Your team gets it immediately.
It Helps You Write Better Detections
When you understand the techniques attackers use, you can build detection rules that catch them. SIEMs like Splunk let you tag alerts with ATT&CK techniques, making it easier to spot patterns. Detection engineering is the discipline of turning that technique knowledge into actual working alerts — it's where TTPs go from theory to practice.
Do You Actually Need to Memorize It?
Nope.
Seriously, no one expects you to memorize hundreds of technique IDs. But you should be familiar with the common ones—especially the tactics like Initial Access, Credential Access, Lateral Movement, and Exfiltration.
When you're learning detection engineering or threat hunting, ATT&CK becomes your go-to reference. "How do attackers usually move laterally?" → Check the Lateral Movement tactic. "What are common persistence techniques?" → Look under Persistence. For a focused look at what actually shows up in SOC work, these are the top ATT&CK techniques analysts encounter most.
How to Actually Learn This Stuff
Start with the tactics, not the techniques. Get comfortable with the 14 main categories first. Once you know the "why," the "what" and "how" make way more sense.
Use it in practice. When you're doing labs, malware analysis, or working through detection challenges, map what you see to ATT&CK techniques. EpicDetect's challenges are tagged with ATT&CK techniques for exactly this reason—you learn by doing, not by reading a giant matrix.
Bookmark the ATT&CK website. Seriously, attack.mitre.org is your best friend. You'll reference it constantly.
TL;DR – TTPs Are Just Attacker Playbooks
TTPs (Tactics, Techniques, Procedures) describe how attackers operate. MITRE ATT&CK organizes all of this into a framework that SOC analysts, threat hunters, and detection engineers use every single day. You don't need to memorize it, but you do need to know how to use it.
---
FAQs
Do I need to know ATT&CK to get a SOC job?
Not necessarily, but it'll definitely help. Interviewers love asking "what MITRE ATT&CK techniques would you expect to see in a ransomware attack?" If you can answer that confidently, you're already ahead of most candidates.
Is there an ATT&CK for other platforms?
Yep! There's ATT&CK for Enterprise (Windows, Linux, macOS), Mobile, and even ICS (Industrial Control Systems). Most SOC jobs focus on Enterprise.
How do I practice using ATT&CK?
Do hands-on labs and challenges. Map the techniques you see to the framework. EpicDetect's malware analysis challenges and detection problems are all tagged with ATT&CK techniques, so you're learning it without even realizing it.
---
Sources & References:
---
Final thought: Understanding TTPs isn't about memorizing technique IDs—it's about thinking like a defender. Once you start seeing attacks as a sequence of tactics and techniques, everything clicks.
How EpicDetect Can Help
Ready to actually learn this stuff hands-on? Head to the EpicDetect Atlas—our skill tree is packed with lessons on threat intelligence, detection engineering, and MITRE ATT&CK. Every challenge is tagged with the relevant techniques so you're learning by doing, not just reading.
New here? Sign up and start learning for free. No credit card required.
Tags
Related Articles
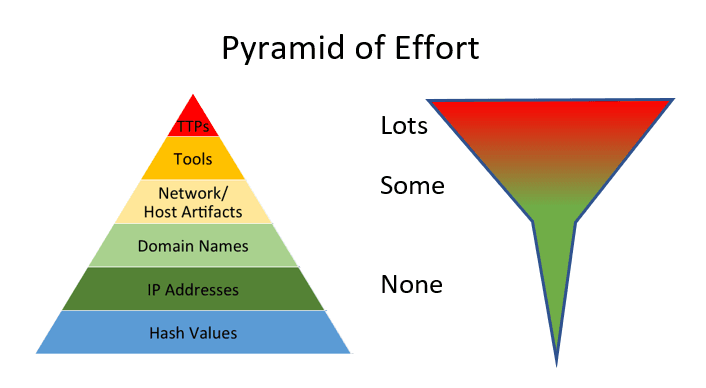
IOCs vs TTPs: What Analysts Actually Hunt With
IOCs are fast. TTPs are durable. Learn the difference between indicators and behaviors—and which one actually matters for long-term threat detection.

The MITRE ATT&CK Techniques You'll Actually Encounter as a SOC Analyst
The ATT&CK matrix has 200+ techniques. Here are the five you'll see on repeat as a SOC analyst—and what to look for when you do.

Detection Engineering 101: What It Is, Why It Matters, and How to Break In
SOC analysts respond to alerts. Detection engineers build them. Here's what detection engineering actually is and how to get into one of blue team's fastest-growing roles.

Why Most SOC Training Fails You (And What Actually Prepares You for Day One)
Certs teach you what things are. They don't teach you how to think. Here's the gap between passing a test and working a real SOC alert—and how to close it.