IOCs vs TTPs: What Analysts Actually Hunt With
IOCs are fast. TTPs are durable. Learn the difference between indicators and behaviors—and which one actually matters for long-term threat detection.
EpicDetect Team
5 min read
IOCs vs TTPs: What Analysts Actually Hunt With
You've seen both terms in every threat intel report, job posting, and security certification. IOCs and TTPs. People throw them around like they're interchangeable. They're not—and understanding the difference will make you a noticeably better analyst.
Quick Definitions (Then We Move On)
IOC (Indicator of Compromise): The artifacts an attack leaves behind. IP addresses, file hashes, domains, URLs, email addresses. Evidence that says "something bad was here."
TTP (Tactic, Technique, Procedure): How the attacker operates. Not what they left, but how they moved. If you want more background on TTPs, check out our TTP explainer—this post focuses on the hunting side.
So Which One Do Analysts Actually Use?
Both. But not equally—and that's the point.
IOCs dominate day-to-day triage because they're fast. A hash match in VirusTotal takes seconds. A known-bad IP in your firewall logs is a quick win. Block it, log it, write the ticket, close the alert.
But for threat hunting and durable detection? Experienced analysts are thinking in TTPs.
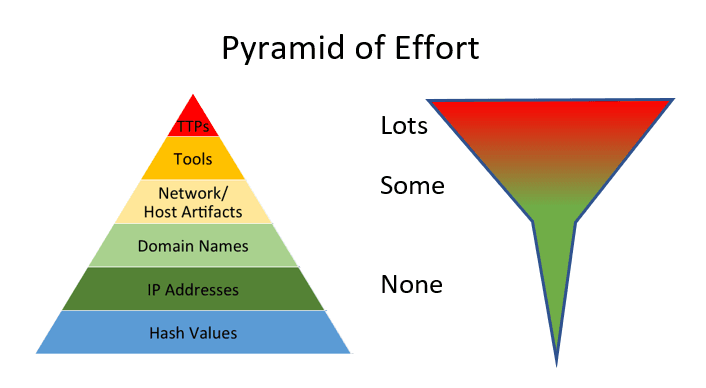
The Pyramid of Pain—And Why It Changes Everything
David Bianco's Pyramid of Pain is one of the most practically useful mental models in threat intel.
- File hashes — trivial to change. Recompile the malware, new hash. The attacker spends five minutes, your detection is dead.
- IP addresses and domains — annoying to change, but attackers rotate infrastructure constantly. Your threat feed is stale faster than you think.
- TTPs — expensive to change. Behavior patterns require retraining, retooling, and rethinking the whole operation. Attackers don't change these often.
The higher you hunt on the pyramid, the more pain you cause the attacker—and the longer your detection stays relevant.
What This Looks Like in an Alert
IOC-based detection: "This IP address appeared in a threat feed."
That detection fails the moment the attacker rotates to a new IP. Which they do. Regularly.
TTP-based detection: "A process spawned cmd.exe, which launched PowerShell, which made an outbound connection."
That detection catches the same attack pattern whether the attacker is using IP A, IP B, or IP Z. Because the behavior didn't change.
This is why detection engineers build behavioral rules. And why smart threat hunters pivot to TTPs when an IOC hunt goes cold. For a deeper dive into building those detections, the detection engineering primer walks through the whole process.
Okay, But Don't Dismiss IOCs
IOCs aren't useless. They're just one layer of a stack.
Use IOCs for:
- Fast triage — quick lookups during active incidents
- Retrospective hunting — searching historical logs for known artifacts
- Context enrichment — adding attribution to an alert ("this hash is associated with Lazarus Group")
- Reporting — stakeholders and leadership love concrete indicators
The smart move is layering them. IOCs for quick wins and context. TTPs for durable, high-fidelity detections that survive infrastructure rotation.
TL;DR – Hunt the Behavior, Not Just the Breadcrumbs
IOCs are fast and easy. TTPs are durable and powerful. Every good analyst uses both—but the ones building long-term detection coverage lean on TTPs.
Start building the habit now: every time you see an IOC, ask yourself what TTP it maps to. That single habit separates reactive triage analysts from proactive hunters.
---
FAQs
Do IOCs from threat feeds actually work?
Yes, especially for commodity threats. But don't rely on them for sophisticated actors—APTs rotate infrastructure constantly. Layer IOCs with behavioral detections.
Where do I even find good TTP mappings?
MITRE ATT&CK is the source of truth. Most SIEMs and EDRs now tag alerts with ATT&CK technique IDs. Get comfortable navigating the matrix. Check out the techniques SOC analysts see most often to prioritize where to start.
Is this relevant for a beginner SOC analyst?
Definitely. Even in tier-1, understanding why you're blocking an IP or escalating an alert matters. It's also a common interview topic—especially for roles at companies with mature security programs. If you're mapping out your full learning path, the 90-day SOC analyst roadmap covers when to tackle this.
---
Sources & References:
- Pyramid of Pain – David Bianco
---
Final thought: The analysts who build the most durable detections aren't the ones with the biggest threat feed subscriptions. They're the ones who understand why attackers behave the way they do—and they hunt the behavior, not the breadcrumbs.
How EpicDetect Can Help
Ready to actually learn this stuff hands-on? Head to the EpicDetect Atlas—our skill tree is packed with lessons on threat intelligence, malware analysis, and MITRE ATT&CK. Every challenge is tagged with the relevant techniques so you're learning by doing, not just reading.
New here? Sign up and start learning for free. No credit card required.
Tags
Related Articles

What the Heck Are TTPs? (And Why Every SOC Interview Asks About Them)
Learn what TTPs are, why MITRE ATT&CK matters, and how understanding them can help you land your first SOC job.

The MITRE ATT&CK Techniques You'll Actually Encounter as a SOC Analyst
The ATT&CK matrix has 200+ techniques. Here are the five you'll see on repeat as a SOC analyst—and what to look for when you do.

Windows Event Log IDs Every SOC Analyst Should Know
The essential Windows Event Log IDs for SOC analysts. Covers Security, System, Sysmon, and PowerShell logs with real-world attack scenarios and MITRE ATT&CK mappings.

What Is Threat Hunting? A Beginner's Guide to Proactive Security
Learn what threat hunting is, why it matters, and how to get started as a beginner. No fancy tools required—just curiosity and the right mindset.